Where AI Innovation Meets Cyber Protection.
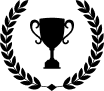
Our proprietary AI-powered dispatching system deploys lightweight agents across Windows, Linux, and macOS devices — silently monitoring processes, network connections, and file changes in real time. When threats are detected — malware, C2 beaconing, lateral movement — the system acts instantly: killing processes, quarantining files, and blocking hostile IPs. All malicious traffic is monitored and blocked in real time — and when the same threat is detected on another device running our EDR, it is proactively blocked across all protected endpoints before the attacker even attempts access. Every incident is classified via MITRE ATT&CK and reported through dashboard alerts, email, and to other partners.
Learn More